We offer two ways to help you understand how Microsoft Azure Single Sign-On (SSO) works in the TIP Tool™ — pick whichever suits you best:
Prefer to watch?
Start with our short walkthrough video that shows how to enable Microsoft Azure SSO and how users can sign in using their Microsoft account.
Prefer to read?
Scroll down for the full written guide with step-by-step explanations.
What Is Microsoft Azure SSO in the TIP Tool™?
Microsoft Azure Single Sign-On (SSO) allows users to sign in to the TIP Tool™ using their Microsoft work account.
Instead of creating and managing a separate password for the TIP Tool™, users can simply select “Sign in with Microsoft” on the login page and authenticate through their Microsoft account.
Once an organization connects its Microsoft Azure account with the TIP Tool™, users who belong to the same Microsoft organization can sign in using their existing credentials and access the platform securely.
Why This Feature Was Introduced
Many organizations manage employee access through Microsoft Azure Active Directory. This allows companies to control authentication, security policies, and user access from a single identity system.
To support this type of enterprise authentication, the TIP Tool™ now provides Microsoft Azure SSO integration. This allows organizations to connect their Microsoft identity system directly with the TIP Tool™.
By enabling Azure SSO, organizations can:
- Allow users to log in using their existing Microsoft work accounts
- Reduce the need to manage separate passwords
- Maintain centralized access control through their Microsoft identity system
This helps organizations simplify access management while ensuring secure authentication for users accessing the TIP Tool™.
Sign Up Using Microsoft Azure SSO in the TIP Tool™ (Step-by-Step)
Follow the steps below to access the TIP Tool™ using Microsoft Azure Single Sign-On (SSO).
Step 1: Go to the TIP Tool™ login page and select Sign in with Microsoft.
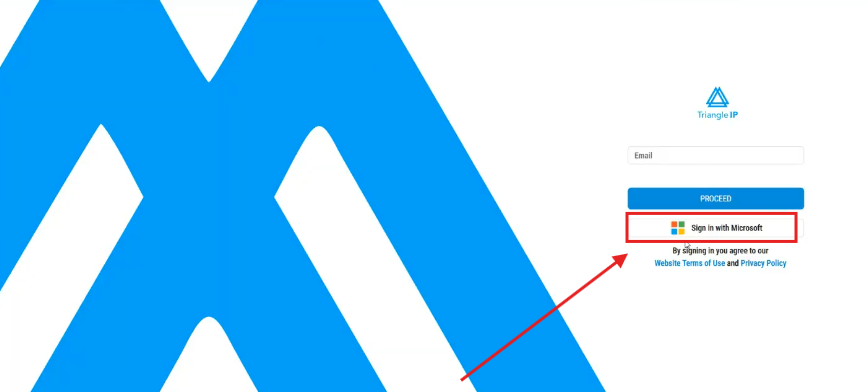
You will be prompted to authenticate using your Microsoft work account.
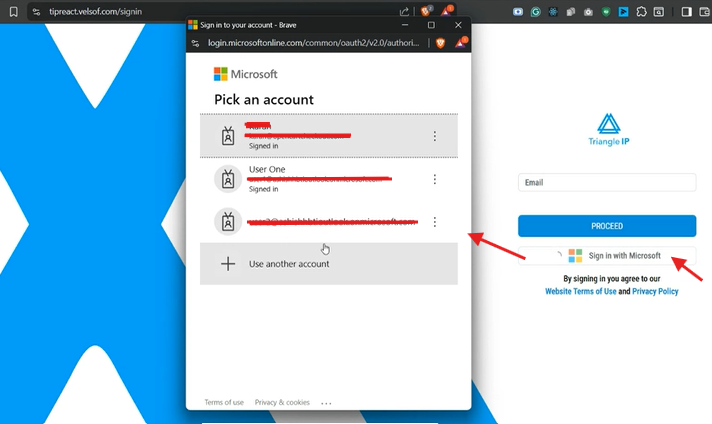
Step 2: Choose the Microsoft account you want to use for authentication.
Microsoft will verify your identity through Azure Single Sign-On (SSO).
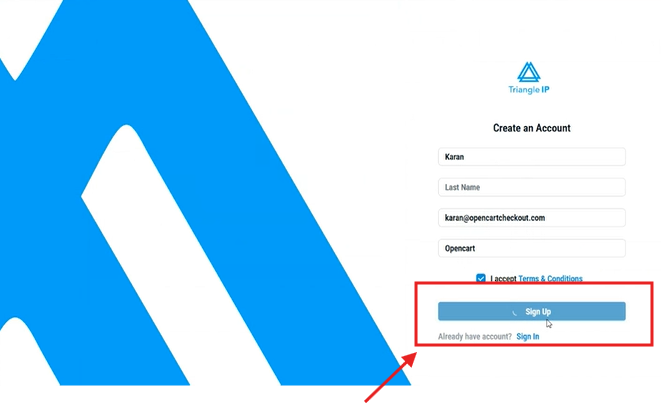
Step 3: If your email does not already exist in the TIP Tool™, you will be redirected to the signup page.
On this page:
- Your First Name
- Email Address
- Enterprise Email
may be automatically filled based on your Microsoft account.
These fields cannot be edited during registration, but they can be updated later in the Profile section after the account is created.
Complete the remaining required fields and click Sign Up to create your account.
Step 4: After completing registration, you can log in directly using Sign in with Microsoft.
Authentication is handled through Microsoft Azure SSO, so you do not need to set or manage a separate password for the TIP Tool™.
Step 5: After clicking Sign Up, a notification message will appear to verifying your email.
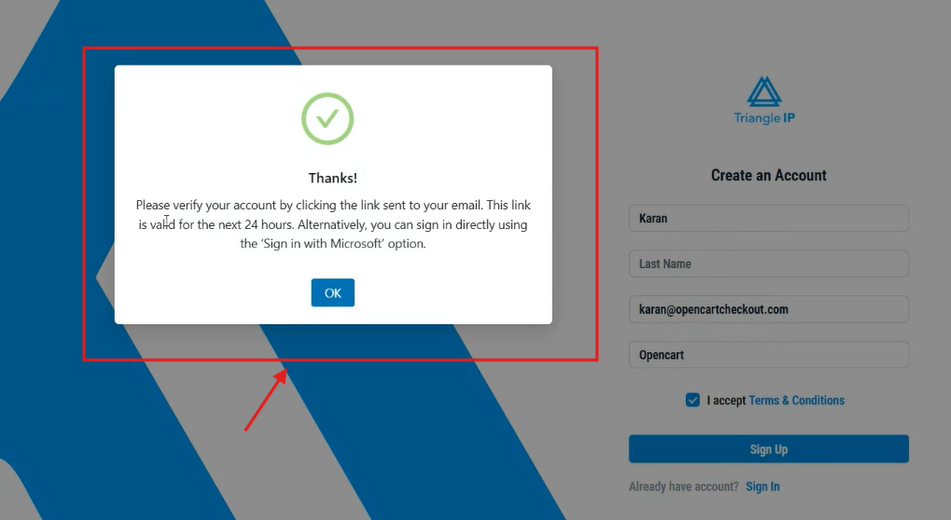
This message indicates that your account registration has been successfully initiated.
Step 6: After verification, return to the TIP Tool™ login page and click Sign in with Microsoft. Select the same Microsoft account you used during registration.
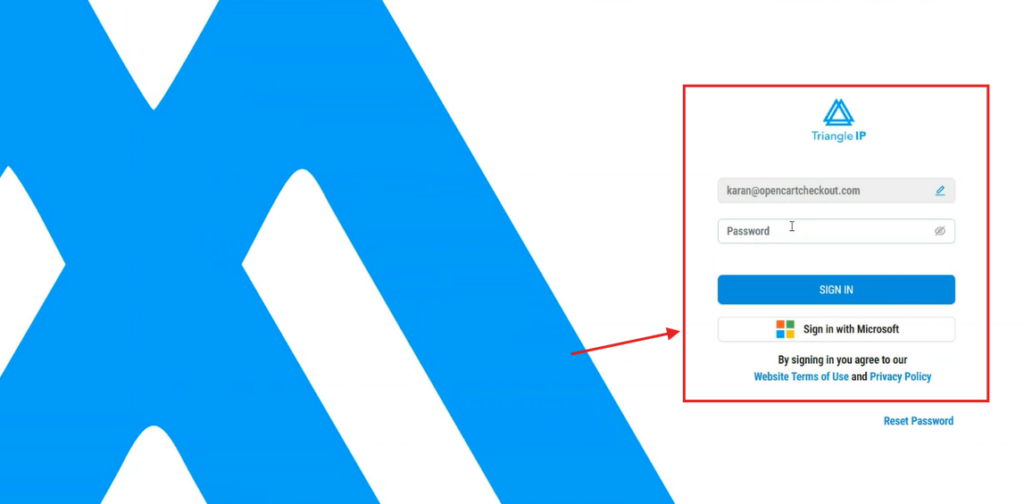
Step 7: Then you will be required to read and accept the Software terms of use. Then click on Proceed.
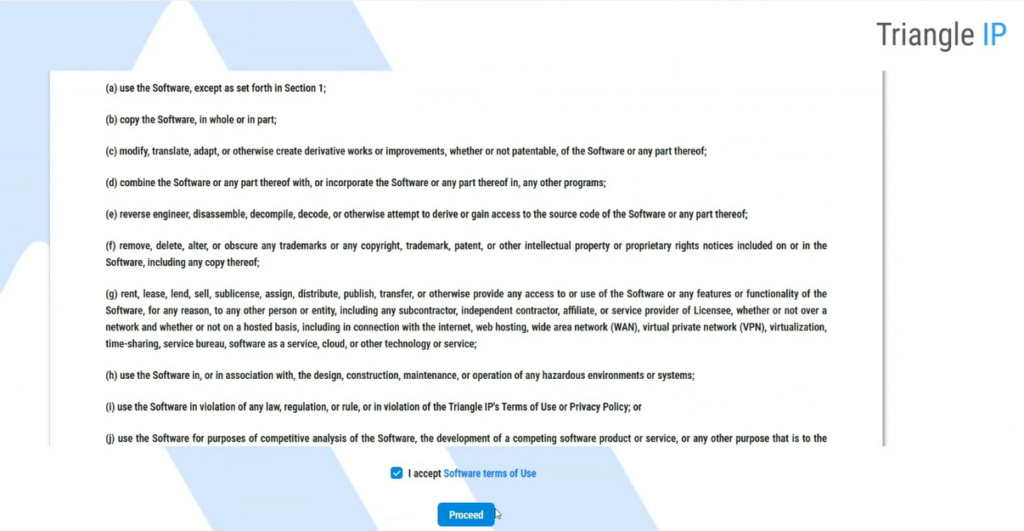
You will then be logged in and redirected to the TIP Tool™ dashboard.
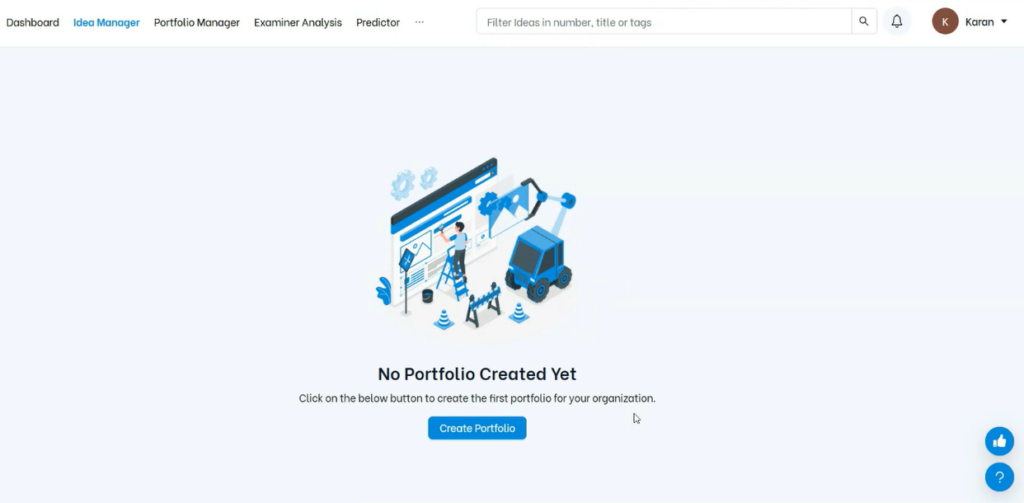
Once users can sign in using Microsoft Azure SSO, organization owners can also connect their TIP Tool™ organization with Microsoft Azure to manage authentication for their team.
The following section explains how to enable Microsoft Azure SSO for your organization.
Enable Microsoft Azure SSO for Your Organization (Step-by-Step)
Organization owners can connect their TIP Tool™ organization with Microsoft Azure Single Sign-On (SSO) to manage how users authenticate when accessing the platform.
Follow the steps below to enable Microsoft Azure SSO for your organization.
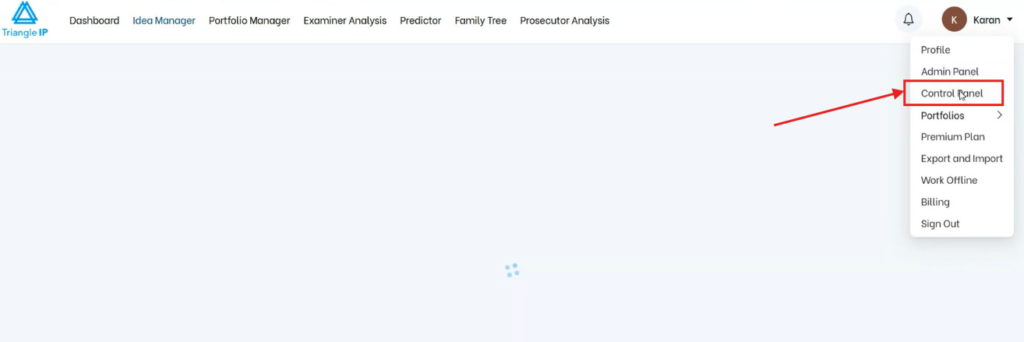
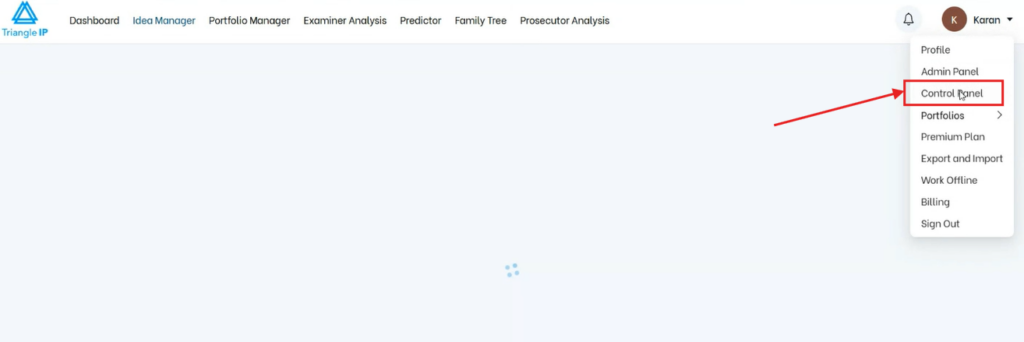
Step 1: Sign in to the TIP Tool™ and open the Control Panel.
Note: Only the organization owner can configure Microsoft Azure SSO settings.
(For demonstration purposes, the steps below were performed using two test portfolios under a single organization OpenCart.)
Step 2: Inside the Control Panel, navigate to Login Settings.
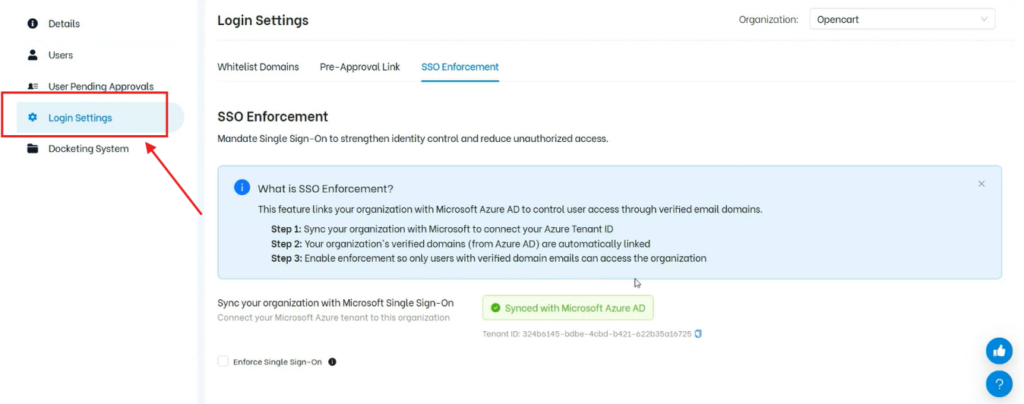
In this section, you will see the SSO Enforcement settings for your organization.
Since we signed up with Microsoft you can see it’s already synced.
If your organization has not yet been connected with Microsoft Azure SSO, you will see the option Sync Now your organization with Microsoft Single Sign-On.
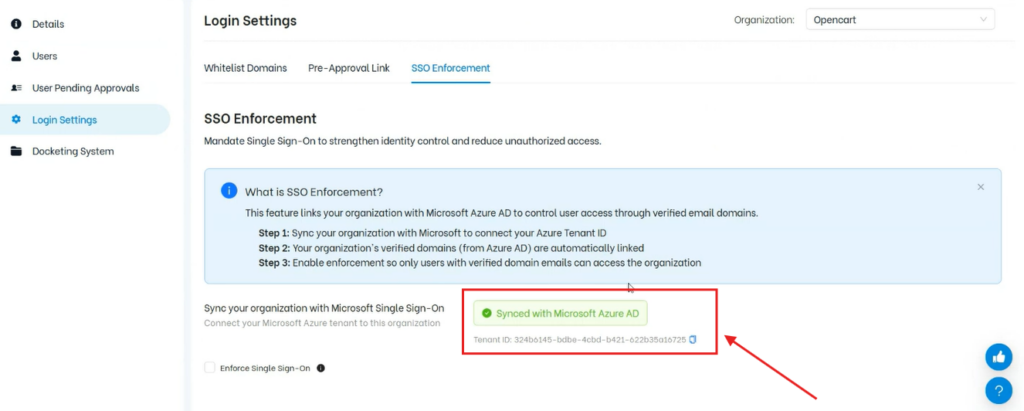
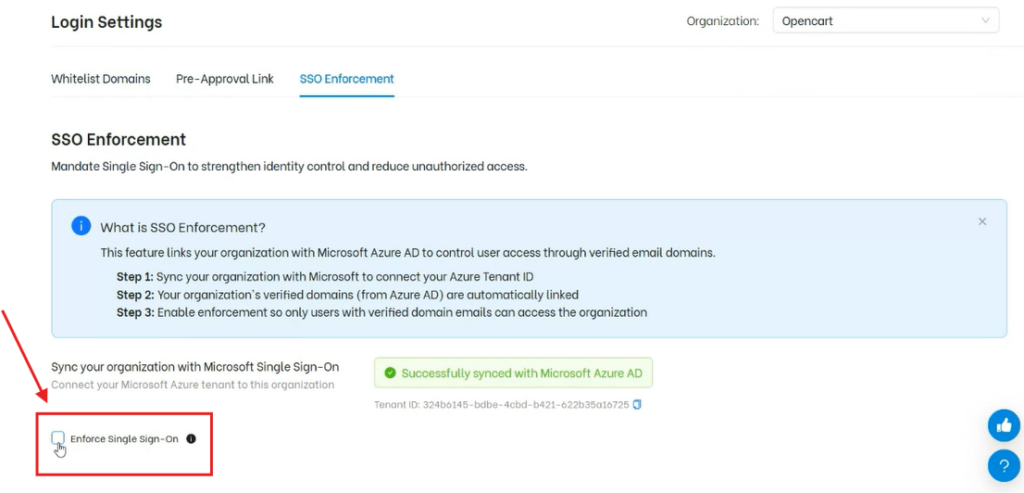
Step 3: Click Sync your organization with Microsoft Single Sign-On.
You will be asked to authenticate using your Microsoft account.
Once the authentication is completed, the TIP Tool™ will connect your organization with Microsoft Azure.
Step 4: After syncing, the system will display the Azure Tenant ID associated with your organization.
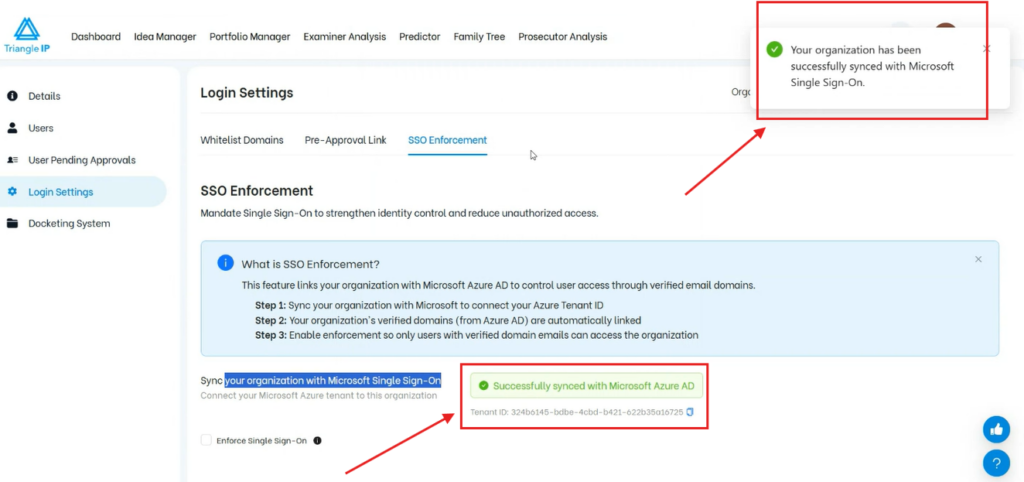
The Tenant ID represents your organization within Microsoft Azure and may include one or more verified domains.
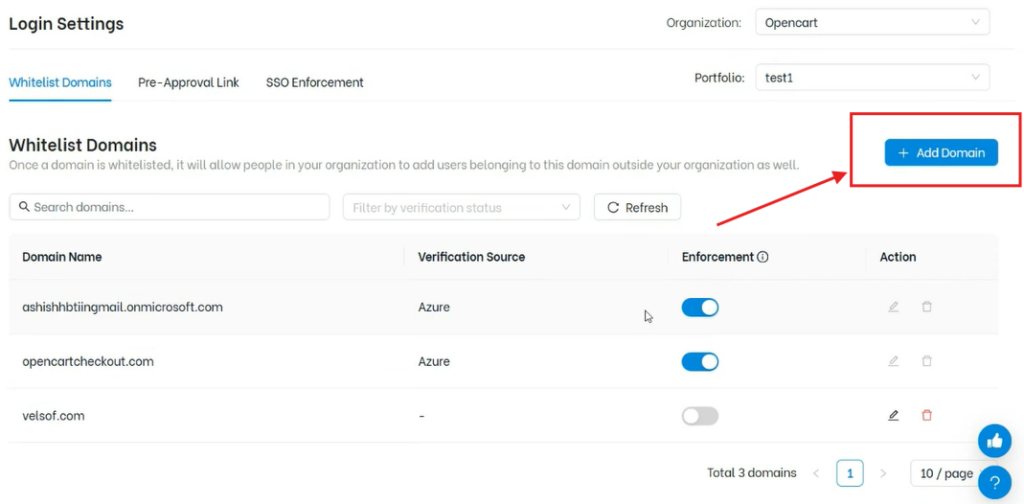
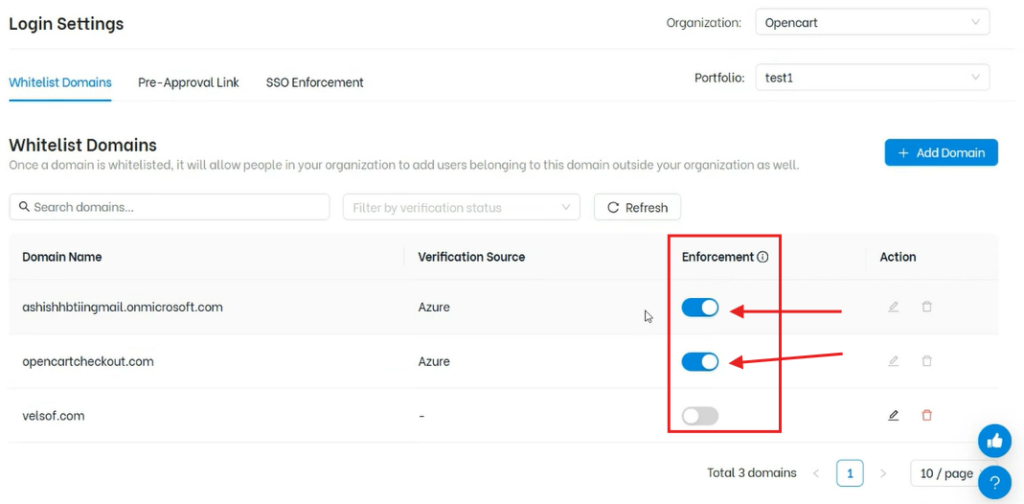
Step 5: Once your organization is synced with Microsoft Azure, the system will display the Azure-verified domains associated with your organization in Whitelist Domains.
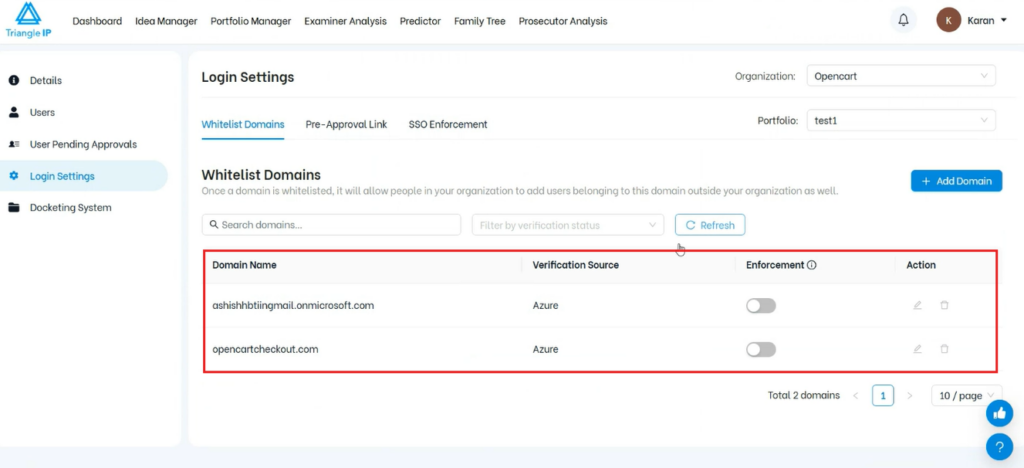
You can enable SSO enforcement for these domains as shown below in the image.
- Only Azure-verified domains can be enforced
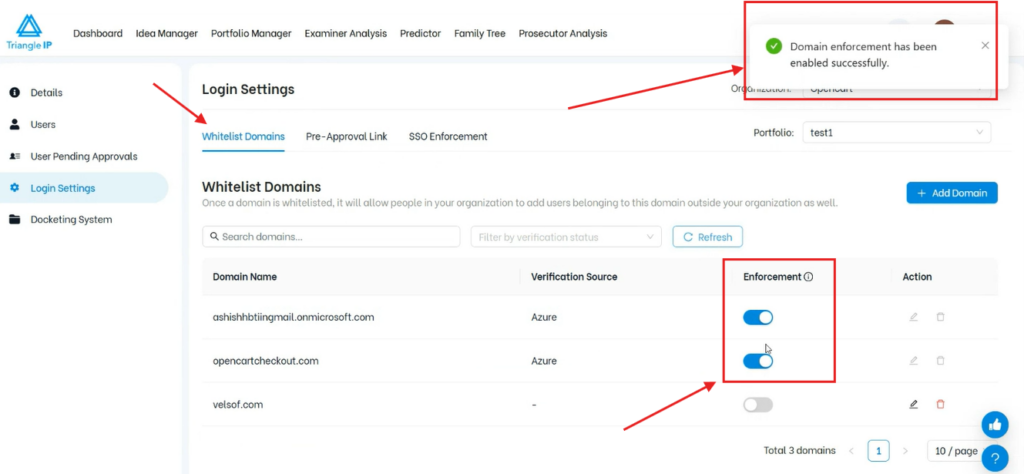
- You may also add additional domains, but enforcement is only allowed for domains verified through Azure
You can turn on enforcement for the selected domain(s) from this switch shown below in the image.
Step 6: Once enforcement is enabled, users from those domains can no longer proceed and log in to the system in the usual way
Instead, they will see a message such as:
Your organization enforces Microsoft SSO for sign-up. Please use Sign in with Microsoft option.
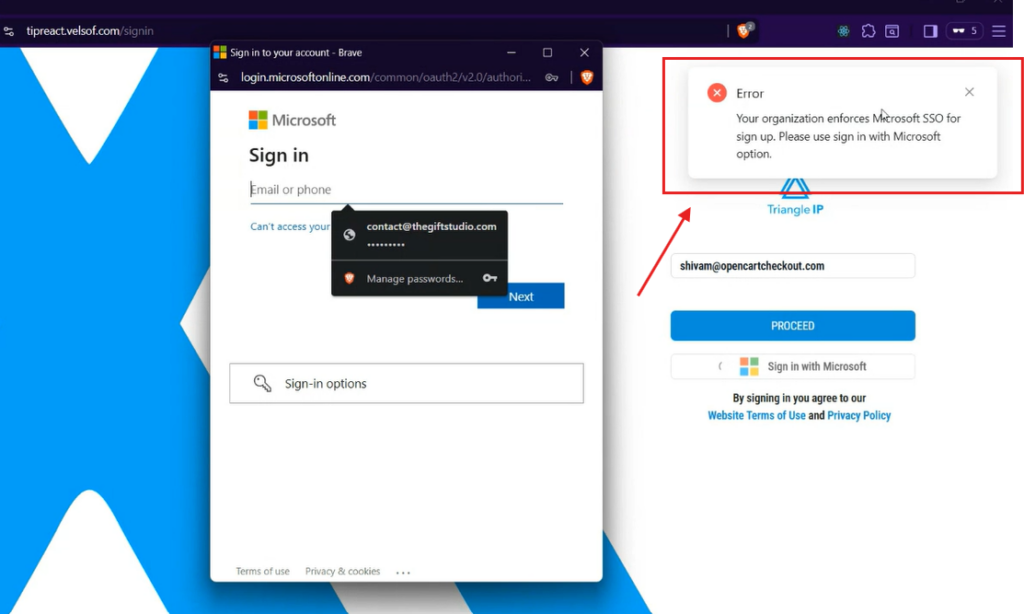
The user must then click Sign in with Microsoft and authenticate using their Microsoft account.
At this stage, instead of creating a new organization, the system identifies that the user belongs to the same Microsoft organization and prompts them to join the existing organization.
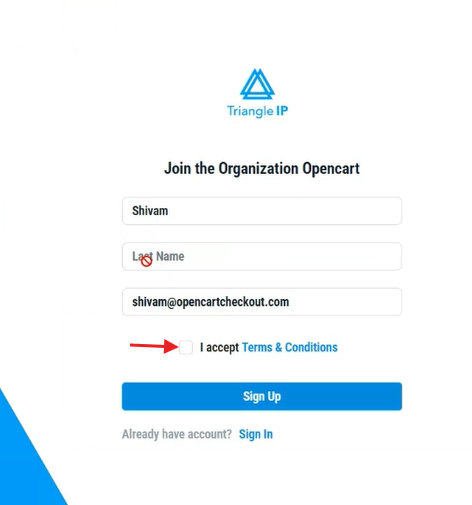
Step 7: After authenticating with Microsoft, the user will be guided through the sign-up flow.
The user must read and accept the Terms & Conditions, then click Sign Up to continue.
Step 8: Once the user completes the sign-up step, a request for approval is generated.
This request is sent to the owner of the organization.
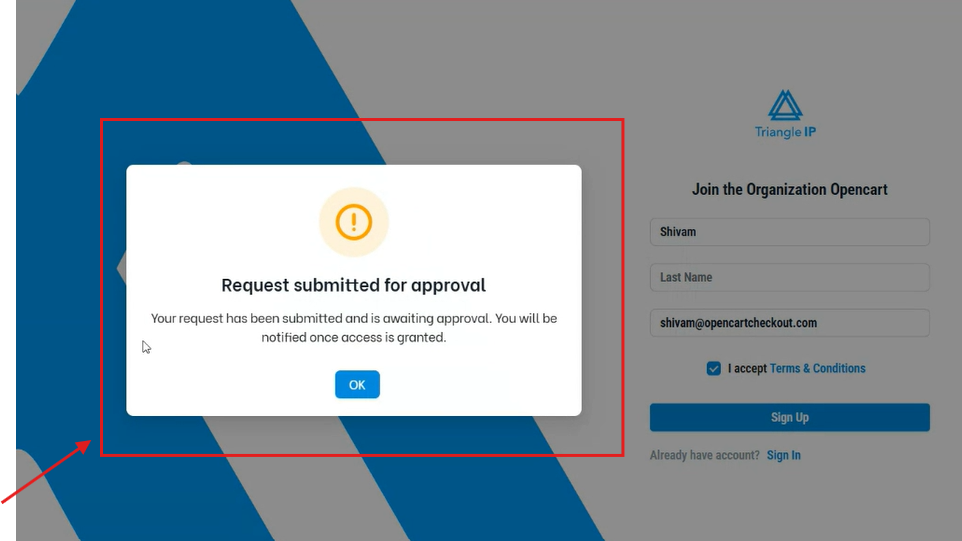
Once the request is submitted, the process moves to the organization owner, who is responsible for reviewing and approving new user access.
The following section explains how the owner can review and approve these requests within the TIP Tool™.
How Approval Works When a New Microsoft User Tries to Join an Existing Organization in the TIP Tool™
When a user from an enforced Microsoft domain signs in with Microsoft Azure SSO and does not already exist in the TIP Tool™, the system does not create a new organization for that user. Instead, the user is prompted to join the existing organization, and a request is sent to the organization owner for approval.
Follow the steps below to understand how that approval process works.
Step 1: The organization owner must sign in to the TIP Tool™ and open the Control Panel.
Step 2: From the left-hand menu in the Control Panel, click on User Pending Approvals.
Here, you will see two sections:
- Pending Requests
- Assign Portfolio to Azure SSO User
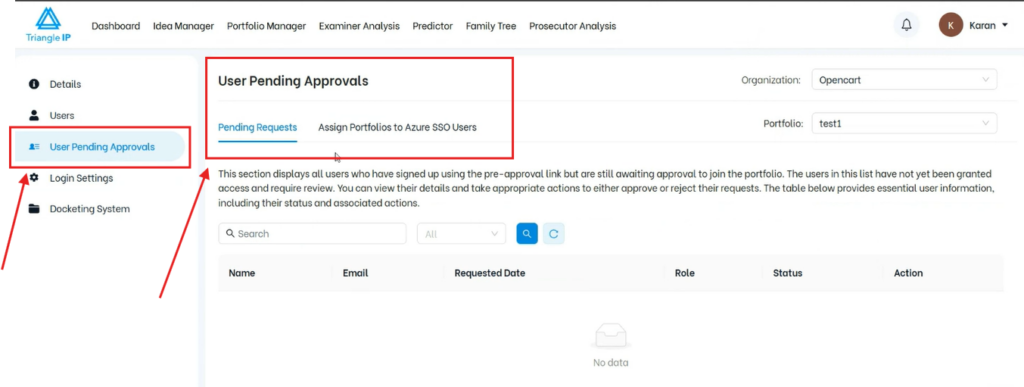
Step 3: Understand the Two Sections
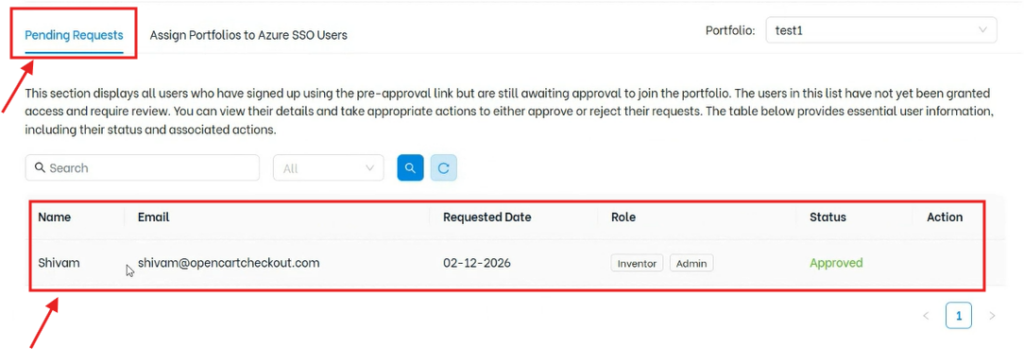
- Pending Requests: This section is used for the existing pre-approval link workflow, where users request access to a specific portfolio.
- Assign Portfolio to Azure SSO User: This section is used for users who sign up using Microsoft Azure SSO and are requesting to join the organization.
The new Microsoft SSO user requests will appear under Assign Portfolio to Azure SSO User.
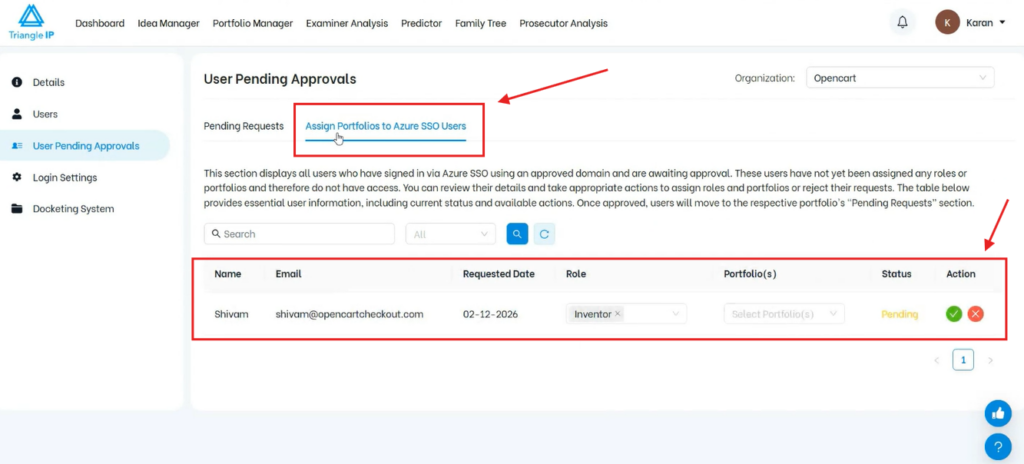
Step 4: The owner can view the details of the user requesting access.
Then the owner must select:
- the portfolio(s) the user should be added to
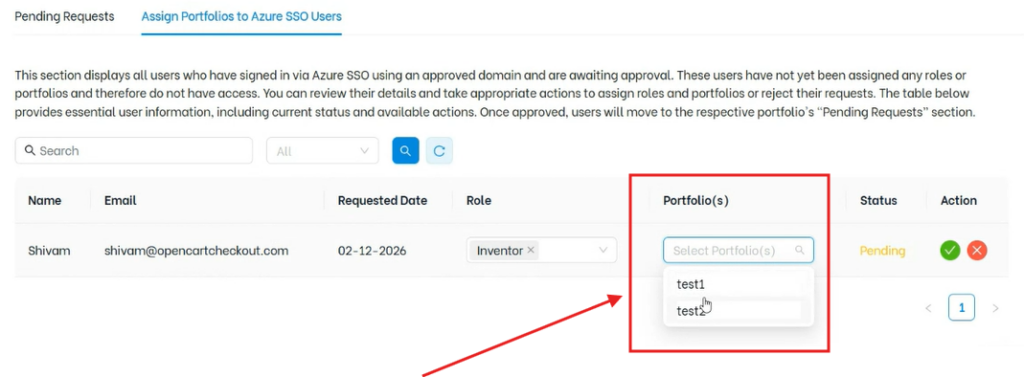
- the role the user should be assigned
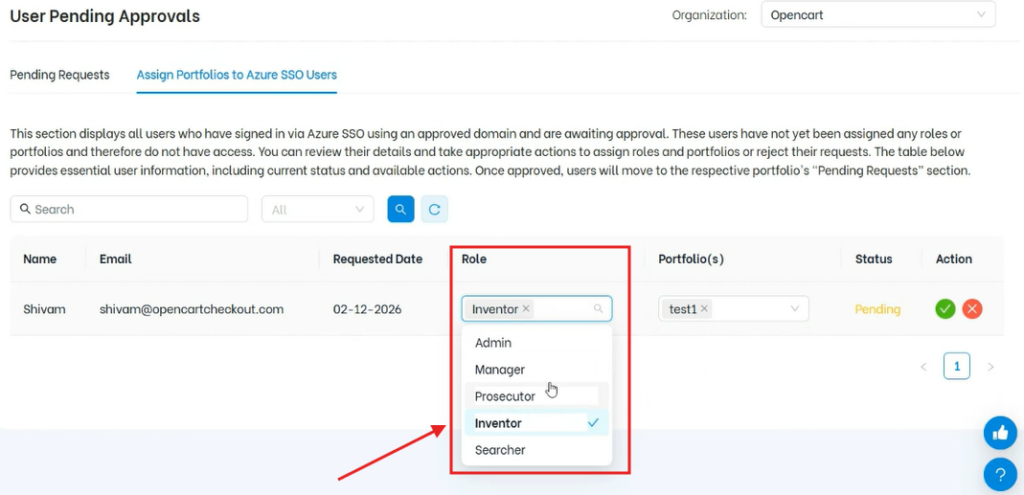
These fields allow the owner to control where the user is added and what level of access they receive.
Step 6: After selecting the portfolio and role, the owner can:
- Approve the request → user is added to the organization
- Reject the request → user is not granted access
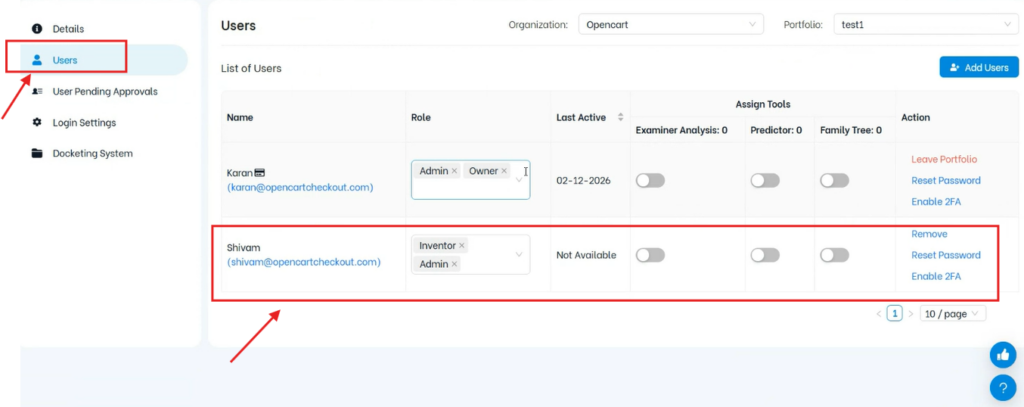
Once approved:
- You will get notified for the status update.
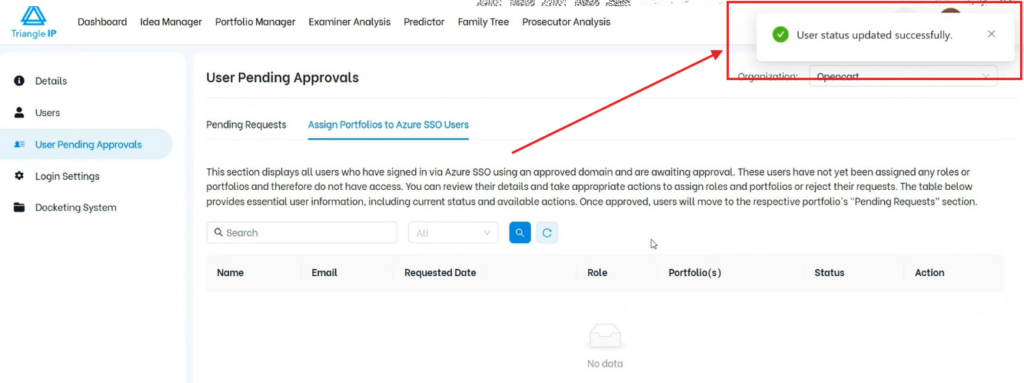
- the user is added to the selected portfolio(s)
- the assigned role is applied
- the user appears in the Users list
To keep a log of requests that user log will be stored in Pending requests.
Quick Recap
- If SSO enforcement is enabled for a domain, users must sign in using Sign in with Microsoft and cannot use the normal login method.
- If SSO enforcement is disabled, users can continue using the standard login flow. New users may create their own account or organization, depending on whether they already exist in the system.